Yes, hacking your app is THAT easy! - Part 2 (iOS File System Analysis)
In Part 1 we looked at Android File System Analysis. We saw how to backup an app using adb, unpack it using abe, then I left it to you to analyze the file system. We also saw how to repack and restore to your device.
In part 2, we will look at iOS File System Analysis. It is a little simpler with iOS, contrary to all the "iOS is more secure..." We can easily access the file system on a non-jailbroken device using some simple tools and take a look at the file system. So sit back, fire up your laptop, and get ready to analyze your app.
- Yes, hacking your app is THAT easy! - Part 3 (Android Network Analysis)
- Yes, hacking your app is THAT easy! - Part 4 (iOS Network Analysis)
- Yes, hacking your app is THAT easy! - Part 5 (Android Source Code Analysis)
- Yes, hacking your app is THAT easy! - Part 6 (iOS Source Code Analysis)
There is a fun little application for your computer called iFunbox (http://dl.i-funbox.com/). With this application we can easily access and manage what apps are installed on our device. While there are more things that iFunbox can do, we will cover the part that is pertinent to file system analysis. (Also make sure that you have iTunes installed)
After iFunbox is installed (or extracted if using the zip file) open it up and connect your iDevice. When you open iFunbox, you will see the following screen. Select iFunbox Classic to see your device and some options.


Then once that is done, open your app, and profit!
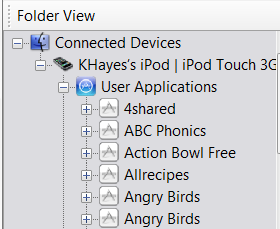
We then can expand User Applications to see a list of applications installed on your device.
If you scroll down and find the app you want to edit, you can click it and see the file structure.
You can then use the Copy To PC option to copy the files to your computer, analyze them, and modify them.
You can then Copy From PC to place the files that you modified back to the device.
That's right. 999,999,999 coins in Hill Climb Racing. That is one simple example, but unlocking levels, vehicles, coins, turning off ads and much more can be accomplished with a little bit of analysis. Until Part 3, Happy Hacking!